Identifying Risks Before Time
We believe in protecting data with advanced methods

RISKS TO WATCH

Reinforcing Information Security – Need of the hour in Africa
Threat Landscape One of the major news channels of South Africa suffered massive data breach compromising data of 60 million users (mostly South African citizens)

How robust is your Password Management?
Do we ever forget or share security numbers of our safety lockers in banks where we keep our precious and valuable items for security? Or

IOTs: Serious cyber risks but we can secure those
IoT (Internet of Things) has made our lives comfortable, easy, smart, exciting and it has spurred innovation too. The boom of IoT in the recent

Protecting health information: Time to be proactive not reactive
More than a week back, Singapore National Public Health Authority revealed that almost 14,000 health records of people from Singapore and other foreign nationals were

The Importance of Privileged Access Management knows no bounds
A young man named Sumit joined an organization as a junior sales associate. The company allotted him a laptop for his daily work activities. Sumit
Privileged Access Management: A Remedy for Data Security
There was a recent data breach incident in one of the global E-commerce giants. Immediately after the news turned epidemic, the management dished out the

Secure Passwords, Save your Digital Assets
Who can forget the infamous data breach incident of one of the popular file hosting service providers where more than 60 million users’ email addresses
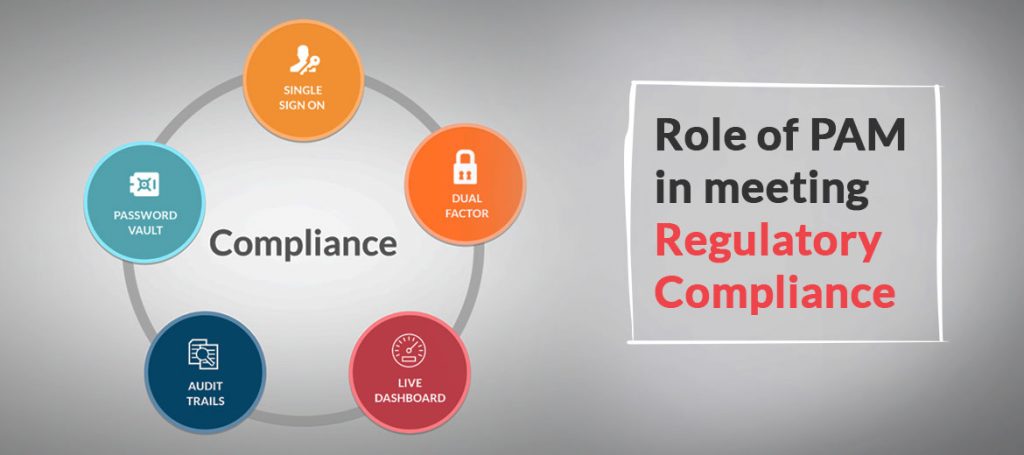
Role of PAM in meeting Regulatory Compliance
Facebook could face penalties worth in billions under GDPR (General Data Protection Act) compliance act for not following the basic policies. It happened because more

How to mitigate misuse of Privileged Accounts
Misuse of privileged accounts is one of the burning threats for enterprises today. The detection process is time-consuming. Even if the organizations try to calculate
