Reinforcing Information Security – Need of the hour in Africa

Threat Landscape One of the major news channels of South Africa suffered massive data breach compromising data of 60 million users (mostly South African citizens) during March 2017. This is considered to be the largest data breach incident in the history of South Africa. Once the hacking news spread like wildfire among the cyber security […]
How robust is your Password Management?

Do we ever forget or share security numbers of our safety lockers in banks where we keep our precious and valuable items for security? Or do we ever share ATM pins or internet banking credentials with anyone? Then why can’t we keep the same habit for securing digital identities? We come across numerous stray incidents […]
IOTs: Serious cyber risks but we can secure those

IoT (Internet of Things) has made our lives comfortable, easy, smart, exciting and it has spurred innovation too. The boom of IoT in the recent past is expected to have a huge amount of monetary involvement that can surpass millions of dollars. Young entrepreneurs have been developing groundbreaking ideas that can take this innovation to […]
Protecting health information: Time to be proactive not reactive

More than a week back, Singapore National Public Health Authority revealed that almost 14,000 health records of people from Singapore and other foreign nationals were compromised and leaked online. “I’m sorry that one of our former staff who was authorized to have access to confidential information in our HIV registry appears to not have complied […]
The Importance of Privileged Access Management knows no bounds

A young man named Sumit joined an organization as a junior sales associate. The company allotted him a laptop for his daily work activities. Sumit found that the laptop was used by the previous employee and it was given to him since he is no more associated with the organization. However, Sumit did not bother […]
Privileged Access Management: A Remedy for Data Security
There was a recent data breach incident in one of the global E-commerce giants. Immediately after the news turned epidemic, the management dished out the queries and criticism and claimed that they have fixed the issue in no time. They even informed the customers who are possibly affected by the ‘breach’ incident. However, it is […]
Secure Passwords, Save your Digital Assets

Who can forget the infamous data breach incident of one of the popular file hosting service providers where more than 60 million users’ email addresses and passwords got affected? An employee just reused a password at work and that was the mistake. The password was broken through to steal the valuable records of the organization. […]
Role of PAM in meeting Regulatory Compliance
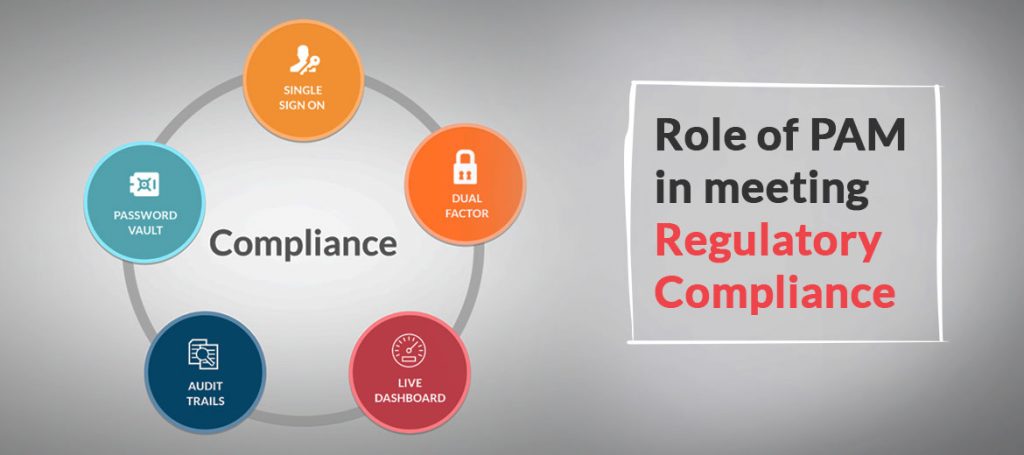
Facebook could face penalties worth in billions under GDPR (General Data Protection Act) compliance act for not following the basic policies. It happened because more than 50 million accounts were compromised due to some negligence from this social media giant. As detected during the end of September, 2018, Facebook unveiled that a particular vulnerability in […]
How to mitigate misuse of Privileged Accounts

Misuse of privileged accounts is one of the burning threats for enterprises today. The detection process is time-consuming. Even if the organizations try to calculate the amount of loss incurred from these threats, it is never possible to get the exact figures because the overall damage is irrevocable – both financial and reputation-wise. 1. Controlling […]
Healthcare Industry: Time to reinforce privileged access control

IT security awareness has become a crying need for the CIOs, CISOs and CTOs of global enterprises. After BFSI, Government, Manufacturing, IT and Pharmaceuticals industry, now Healthcare industry is facing the wrath of Cyber criminals. Off late healthcare sector has become a lucrative target for those who target compromised privileged accounts to steal sensitive information. […]
