The #1 Converged Identity Platform for Securing Global Enterprises
Recognised by Global Analysts as the Leader in the Enterprise Identity Security Domain. Seamlessly Protecting millions of identities for 1500+ organizations spread across 6 continents. Enhance Your Resilience and Security Posture with Premier Risk Management Solutions / built on a Zero-Trust Architecture.


The future is Digital. We are on a mission to protect your identity, ideas and privacy
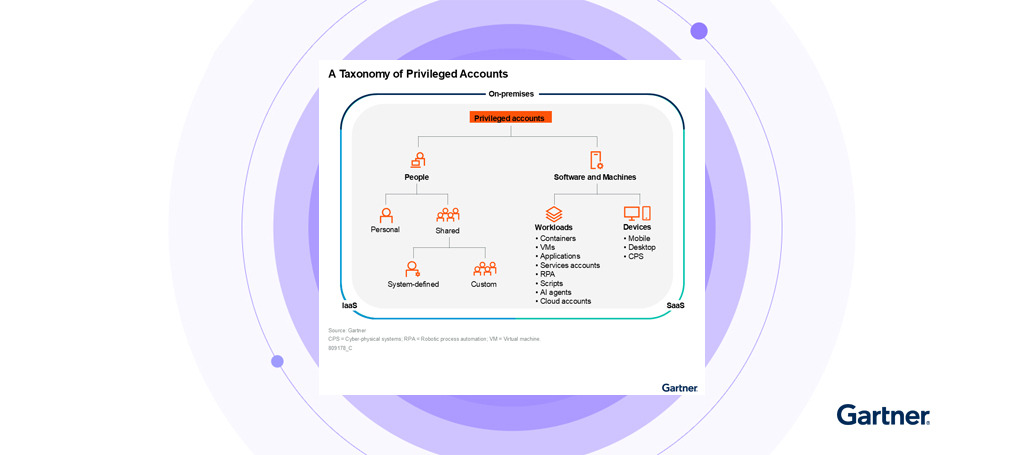
Digital Identities play a central role in our hyper-digital world. Us as humans, and every device we interact with – cars, machines, chips, phones, computers – are unique digital identities.
As IT converges, the relevance is further increased with the advent of IoT/OT devices. Soon, we will need to protect intelligence (AI/ML Models). This will have an impact that we cannot even bring ourselves to imagine yet.
Digital Identities are the most common attack vector. We need to protect them. Here’s how you can!
Ring-Fence your core digital Infrastructure
ARCON | PAM creates a perimeter for your core digital assets, whether they are technologies like OS, DB, web servers, network equipment, telecom devices, Wi-Fi devices, security devices, operational technologies, IoTs, or human elements in your organization’s IT environment. Access to these devices is heavily regulated and only allowed through security gateways installed at the perimeter, taking away the load on firewall-rule engines.
ARCON provides a unified experience for all identities through its access management solutions – interactive and non-interactive IDs, machine IDs, or embedded IDs. These solutions cover all business applications, infrastructure devices, cloud assets, and even identities embedded in software assets.
Secure your digital assets
Taking over from machines, identities now hold the mantle as the critical asset that require stringent protection – an effect that is amplified by the sheer number of endpoints that have emerged as a consequence of the new Work From Anywhere (WFA) business culture.
What organizations now need to do is ensure that the identities in their IT environment are doing only what they need to or what they are authorized to do, especially when data is involved. With millions of identities and an ever-expanding data bank, you need super-intelligent solutions like ARCON | EPM – constantly learning and adapting to create a circle of trust that can keep a vigilant eye on all your various endpoints.

Data is like water. A drop is an Ocean moves, mixes, and merges with the old to create something new
Security experts have to assess the need for specific data and data-access intricacies in a translucent world. You may have to spend millions protecting that which is not even contextually important. To follow the next generation security principles, you must follow the trail of your data.
ARCON provides you with this deep insight into data, including what you have, what is important, where it rests, when it moves, and its contextual meaning.
Learn More
Our Customers







In the News
Identiverse 2026
Event Organizer: Identiverse
Event Name: Identiverse 2026
Date: June 15-18, 2026
Venue: Mandalay Bay, Las Vegas, Nevada, USA
Booth: #438
Identity Week 2026
Event Organizer: Identity Week
Event Name: Identity Week 2026
Date: June 9-10, 2026
Venue: RAI Amsterdam, Netherlands
Booth: #1201
Gartner IT Infrastructure, Operations & Cloud Strategies Conference 2026
Event Organizer: Gartner
Event Name: Gartner IT Infrastructure, Operations & Cloud Strategies Conference
Date: June 1-2, 2026
Venue: Grand Hyatt, Mumbai, India
Booth: #304