Converged Identity Platform
The #1 Converged Identity Platform
In the backdrop of fast-paced digitalization drives, increasing IT complexities and expanding cyber threat attack vector, the boards are demanding improved cyber security posture.
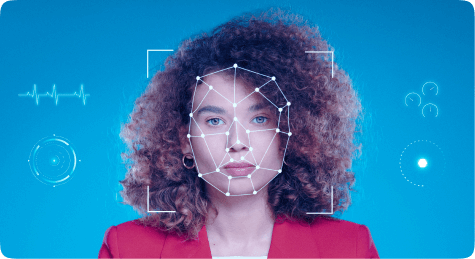
Identity-first security for a robust cyber security posture, and compliance
At a time when organizations are witnessing massive identity sprawls amid large-scale cloud adoption, process automations, OT, and IT convergence, and increasing IoT device identities, the security of a digital identity will be of paramount importance.

Fragmented Identities: It is time to build a perimeter for every digital identity
Building an identity-fabric is a foundational step toward constructing an identity-first and the Zero Trust security posture. It ensures that IAM pros have a set of procedures to effectively manage, control, and govern users, machine identities and their entitlements.
Building an Identity Fabric
By implementing ARCON Converged Identity platform, organizations can establish an integrated identity fabric that provides continuous and context-aware controls as well as centralized management and governance of decentralized identities, a core requirement of the Zero Trust framework.

Security, Administrative Efficiency and Scalability ensured by ARCON | Converged Identity Platform
ARCON | Converged Identity Platform
The first and a truly native converged identity suite that provides out-of-box integrations, intuitive workflow matrix, and powerful reporting mechanism along with robust governing engine.
As ARCON Converged Identity is a natively built single vendor solution, it removes the complexities of managing multiple IAM solutions, enhancing IT administrative efficiency and lowering the operational cost.
With ARCON, the organization’s “Convergence” program will be highly successful as the CI (Converged Identity) suite has strong integration with Endpoint Management.
The platform provides the most mature and the best-in-class password vault which provides seamless password randomization, secrets, and password management capabilities.
The ARCON CI suite comes with many built-in connectors, enabling swift integration and scalability.
ARCON offers flexible deployment models- SaaS-delivered as well as on- premises deployments to suit organizations’ needs and requirements.
Any ordinary Converged Identity solution
An ordinary converged identity solution is built in parts, that is, no single vendor offering. Multiple tools from different offerings results in lack of integration and implementation.
The whole idea of a holistic management of distinct and many identities through a unified engine would never become a reality as separate IAM, IGA, PAM modules will require strong integrations which is a complex task, resulting in higher operational costs.
An ordinary CI solution offers just a few IAM functionalities while endpoint management is lacking.
An ordinary converged identity solution lacks comprehensive credentials management capability that can hamper the security and compliance posture.
It offers limited connectors, hampering an organization’s scalability.
An ordinary CI solution lacks deployment flexibility.

ARCON Unified IAM Approach
A unified IAM approach provides complete observability of a digital identity environment and a centralized engine for administering dynamic human and non-human identity-based use cases.
“By 2025, 70% of new access management, governance, administration and privileged access deployments will converge identity and access management platforms.”
– Gartner report titled ‘Predicts 2022: Identity-First Security Demands
Decentralized Enforcement and Centralized Control’
Decentralized Enforcement and Centralized Control’
ARCON provides a converged IAM platform, covering all core areas of IAM, including IGA, Access Management and PAM, but also providing Password Management capabilities, support for Enterprise Single Sign-On, and the ability to manage endpoints to a certain level.
– Martin Kuppinger, Principal Analyst KuppingerCole AG

