10 Best Practices for PAM solution
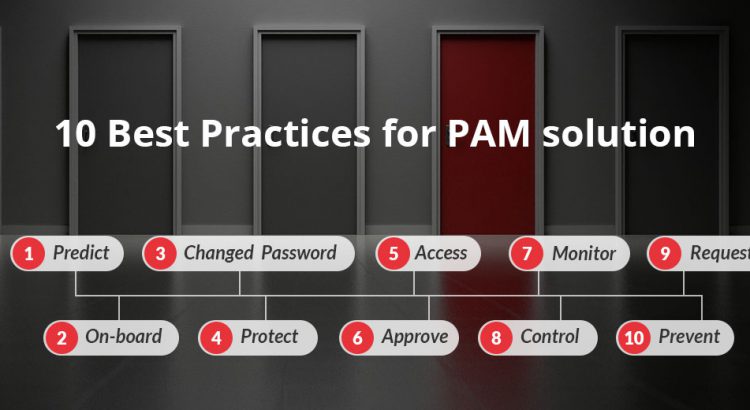
Privileged Access Management (PAM) is one of the most discussed area of today’s cyber security arena. With the increased number of alarming data breach scenarios worldwide, it is very obvious that PAM solution would shield the organizations from any threats arising from unmonitored accounts or poor access control system. Here is a brief account of […]
