
How Privileged Access Management Ensures IT Agility
Overview “Agility is the ability to adapt and respond to change… agile organizations view change as an opportunity, not threat.” -Jim Highsmith, software engineer

Overview “Agility is the ability to adapt and respond to change… agile organizations view change as an opportunity, not threat.” -Jim Highsmith, software engineer

Privileged account attack is a specific kind of cyberattack used to gain unauthorized access to a secured perimeter, which can also be used to obtain

In the wake of expanding IT infrastructure, today’s organizations require their employees to access multiple applications to perform day-to-day IT administrative and operational activities. That

Revolutionary technologies such as Internet of Things (IoTs) and cloud computing, AI, Big Data, et al have created enormous opportunities for global organizations. They have

Overview Can we think of an organization that does not have any segmentation of departments like marketing, finance, HR & Administration? The answer is probably

Probably there are more number of digital identities today than the human population on this planet. Indeed, digital identities have spiralled as our modern day
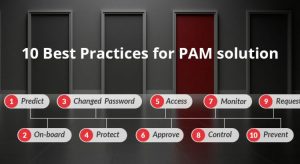
Privileged Access Management (PAM) is one of the most discussed area of today’s cyber security arena. With the increased number of alarming data breach scenarios

Defying the enemy within As the wave of digitization sweeps across the nation, it is terribly crucial for the organizations, irrespective of large or small,

We have been touring across the world since the beginning of the year, participating in several IT security events. While our main goal is to

Andrew Dalglish, director of Circle Research, a UK based research firm recently said “The very people working in businesses can pose as the biggest threat
Please complete this form to join the ARCON community and secure your digital future! Look for an email to confirm your subscription!
ARCON is a globally recognized Identity-As-A-Service provider with a wealth of experience in risk management and continuous risk assessment tools. Our award-winning solutions portfolio includes our Privileged Access Management (PAM) solution along with Identity and Access Management (IAM), Endpoint Privilege Management (EPM), and Cloud Governance (CIEM), among others. Our world-class training, deployment, and support help organizations optimize their experience with our solutions right from the procurement stage and configure our solutions to match all challenges to support growth and scalability.
ARCON. All rights reserved. Copyright 2026 ARCON
Feel free to drop us an email, and we will do our best to get back to you within 24 hours.