Identifying Risks Before Time
We believe in protecting data with advanced methods

RISKS TO WATCH

Social Engineering and Data Breach
There is no question regarding how technically highly-advanced and sophisticated cyber-criminals are. They possess adequate skills and know-how to intrude inside the IT network and

Misinformation, Disinformation, and Misinterpretation
Much is being discussed about the security vulnerabilities in the healthcare industry. As the global digital healthcare system finds itself on the cusp of digital

When Bad AI takes on Good AI
In the vast compass of the digitalized world, the good actors often meet roadblocks created by bad actors. The later, as always, want to create

It’s not just about changing passwords
Alright, passwords are changed regularly and all the updates are being installed unfailingly. Our devices are safe and secure, and the data is going nowhere.

Time to Nurture Cybersecurity Pros
Earlier this year, a bizarre cybercrime shook the world. A story broke of a criminal gang known as Fin7 faking a company to recruit potential

Risks, Compliance and Emerging perils
The fallout of financial frauds in the cryptocurrency industry could be devastating and finally regulators are taking note of it. Indeed, regulators are scurrying to
Identity Governance: How to keep the House in Order?
Probably the most convoluted IT practices of all, the Identity Management and Governance is always vulnerable to a security gap. After all, controlling a vast
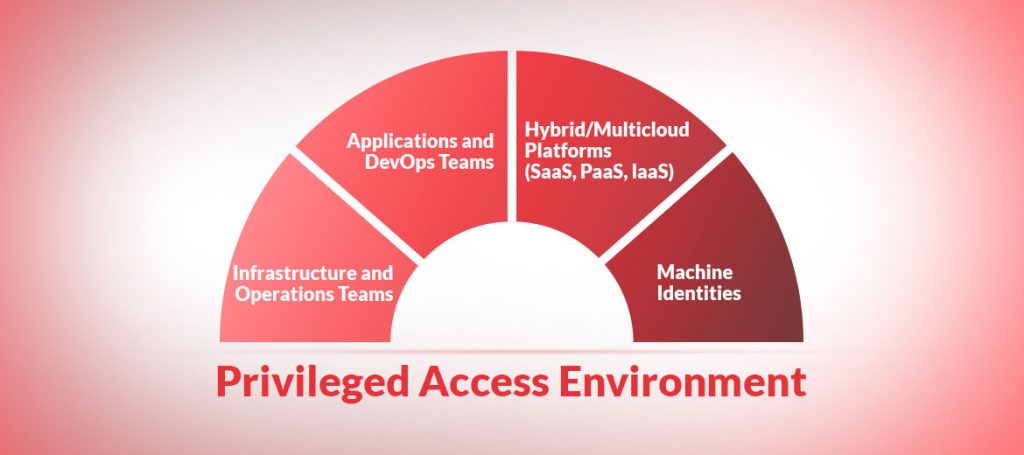
PAM, People and Processes
That the effectiveness of a PAM tool is only as good as the organization’s outline around its PAM practice was never so true as today.

How to Ensure Robust Compliance and IT Audits?
Enterprise IT vulnerability assessment in a timely manner is one of the basic requirements to ensure a robust IT security framework. And IT audits and
